Spy : Cyber Espionage War, Global Intelligence Clash, Security Alert Surge

You sai
In the digital era where borders blur online and critical systems operate in cyberspace, cyber espionage has emerged as one of the most consequential arenas of 21st-century conflict. From nation-state intelligence operations, clandestine data theft, to sophisticated malware campaigns that disrupt entire infrastructures, the cyber espionage war is reshaping how countries fight, protect secrets, and maintain global power.
This comprehensive article explores the escalation of cyber espionage, examples of major operations, ongoing security alert surges, and how global intelligence agencies respond in an increasingly volatile digital battleground.
What is Cyber Espionage?
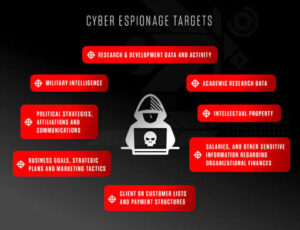
Cyber espionage — often termed cyber spying — refers to the clandestine use of digital tools and techniques by governments, organized hacker groups, or state-linked actors to infiltrate targeted networks and steal confidential information, monitor activities, or gain strategic advantages without detection.
Unlike traditional human intelligence (HUMINT), cyber espionage operates entirely through networks, malware, vulnerabilities, and social engineering, making it more secretive, scalable, and harder to attribute. The stakes include military secrets, economic intelligence, diplomatic communications, and critical infrastructure blueprints.
The Explosion of Cyber Espionage Threats
Recent threat intelligence reports show a dramatic rise in cyber espionage incidents worldwide — driven by geopolitical tensions, technological advancements like AI, and aggressive strategies by nation-state actors. According to cybersecurity research, China-linked actors alone have driven up cyber espionage attacks by over 150%, leveraging advanced social engineering and AI-enabled tools to evade detection and infiltrate networks.
Additionally, international cybersecurity firms have reported massive global campaigns affecting dozens of countries, signaling that these operations are no longer isolated but part of a broader global intelligence clash.
Why Cyber Espionage Matters
Cyber espionage matters for several critical reasons:
1. National Security Risks
When foreign actors infiltrate military or government systems, the damage can be devastating. Historical campaigns such as Moonlight Maze, one of the first known large-scale cyber espionage operations, compromised U.S. defense data and sensitive military information in the late 1990s — demonstrating how digital intrusions can impact national security.
2. Economic & Strategic Advantage
Corporate and technological secrets are now prized targets. Nations invest heavily in cyber intelligence to steal intellectual property, revealing trade policy plans, emerging technology data, or economic strategies. The consequences include lost competitiveness and weakened strategic positioning on the world stage.
3. Infrastructure Vulnerability
Critical infrastructure such as power grids, communications systems, and government networks are high-value targets. The broader trend is not only theft but disruption, where cyberattacks can cripple services and erode public trust.
Notable Cyber Espionage Campaigns
🕵️♂️ GhostNet and the Shadow Network
In one of the earliest documented large cyber espionage operations, GhostNet infiltrated high-value political, media, and diplomatic systems across more than 100 countries, exposing sensitive information and strained diplomatic relations.
Similarly, the Shadow Network was discovered compromising government networks such as those linked to Tibet and Indian officials — highlighting cyber espionage’s ability to bypass traditional defenses through cloud services and social platforms.
🐍 Advanced Persistent Threat (APT) Groups
State-linked hacker groups such as APT28 (“Fancy Bear”) and APT29 (“Cozy Bear”) have been tied to major espionage incidents, including breaches of political networks and cloud services.
These groups exemplify how modern cyber espionage blends stealth, long-term infiltration, and resilience against defensive efforts.
🛠 State-Linked Malware and Operations
Government intelligence units are not just targets — they are often operators of sophisticated cyber tools. The Equation Group, believed tied to U.S. intelligence, is one such example where state capability matches or exceeds those of adversaries.
In other cases, insider threats — where individuals with access to sensitive systems sell or leak intelligence — pose another dimension to the espionage landscape, as seen in real-world prosecutions involving intelligence personnel.
Recent Surges in Cyber Security Alerts
Cybersecurity alerts are rising globally, with attacks increasing in frequency and complexity:
📈 State-Backed AI-Enhanced Campaigns
Nations like Russia, China, Iran, and North Korea are integrating AI into cyber operations to automate attacks, craft deepfake phishing attacks, and bypass legacy security systems — causing significant spikes in digital threats.
🌍 Widespread Cyber Espionage Blasts
Operations have spanned continents, with some campaigns compromising 70 organizations across 37 countries, pointing to expansive reconnaissance and intelligence collection efforts.
🧠 Innovation in Dark Operations
Recent incidents also involve exploiting AI systems themselves for espionage — such as a Chinese hacker group leveraging an AI platform to carry out attacks against global institutions — underlining the evolving nature of cyber threats.
How Nations Respond to the Cyber Espionage War
Governments and agencies worldwide are escalating cyber defenses and counterintelligence postures:
🛡 Strengthening National Cyber Strategies
Many countries now treat cyber espionage as a national defense priority, integrating cyber commands, secure cloud architecture, and rapid response teams to intercept intrusions.
🤝 International Collaboration
Global alliances are forming to share threat intelligence, best practices, and coordinated defenses to mitigate cross-border attacks.
🚨 Public Alert Systems
Security agencies issue regular advisories to businesses and citizens on active threats, recommended patching, and improved identity defenses.
The Human Factor: Insider Threats and Espionage
Beyond technical exploits, human insiders remain a persistent risk. Individuals with access to classified systems can unintentionally or maliciously leak data, making insider threat programs vital components of any cybersecurity framework.
Organizations now invest in controlled access, behavioral analytics, and multifactor authentication to reduce such risks.
Future Trends in Cyber Espionage
As technology evolves, so will the tactics of espionage:
📡 AI-Aided Exploitation
Machine learning tools will increasingly scan for vulnerabilities, craft convincing social engineering attacks, and adapt in real time to defensive measures.
🌐 Quantum & Cryptographic Threats
Emerging quantum technologies may challenge current encryption standards, potentially allowing future intelligence operations to break secure communications.
⚖ Cyber Diplomacy & Norms
International treaties and cyber conventions may emerge to establish conduct standards — but enforcement remains complex.
Conclusion: Staying Vigilant in a Digital Warzone
The cyber espionage war is not a distant threat — it is a present, pervasive conflict shaping global intelligence dynamics. From state actors with vast resources to sophisticated AI-enabled operations, the surge in security alerts signals an urgent need for robust defenses, international cooperation, and public-private alignment.
Whether you’re a government, business leader, or cybersecurity professional, understanding this landscape is critical to safeguarding data, protecting infrastructure, and maintaining strategic advantage in the digital era.
📌 FAQs (Frequently Asked Questions)
1. What is cyber espionage?
Cyber espionage is the use of digital technologies to secretly infiltrate and steal information from systems, networks, or individuals — typically on behalf of state actors or organized groups.
2. How do cyber espionage attacks start?
Most begin with social engineering (like phishing), exploiting software vulnerabilities, or insider compromise to gain initial access to a target network.
3. Which countries are commonly involved in cyber espionage?
Major state-linked actors include China, Russia, Iran, North Korea, and others — each using cyber capabilities to gather intelligence, exert geopolitical pressure, or steal critical data.
4. Can businesses protect themselves from these threats?
Yes — through layered security (firewalls, VPNs, endpoint detection), employee training, threat intelligence feeds, and regular security audits.
5. What is the future of cyber espionage?
Expect more AI-assisted attacks, evolving threats against cloud infrastructure, deeper global intelligence clashes, and continued investment in defensive capabilities.
How useful was this post?
Click on a star to rate it!
Average rating 0 / 5. Vote count: 0
No votes so far! Be the first to rate this post.
About the Author
usa5911.com
Administrator
Hi, I’m Gurdeep Singh, a professional content writer from India with over 3 years of experience in the field. I specialize in covering U.S. politics, delivering timely and engaging content tailored specifically for an American audience. Along with my dedicated team, we track and report on all the latest political trends, news, and in-depth analysis shaping the United States today. Our goal is to provide clear, factual, and compelling content that keeps readers informed and engaged with the ever-changing political landscape.



